The HIPAA, or Health Insurance Portability and Accountability Act, was put into place in 1996 to protect sensitive patient data. It’s standards preserve medical health records and other personal health information so that people can continue to hold health insurance coverage, as well as their privacy. Still, HIPAA standards are not just devoted to the health industry. So, who should be HIPAA-compliant?
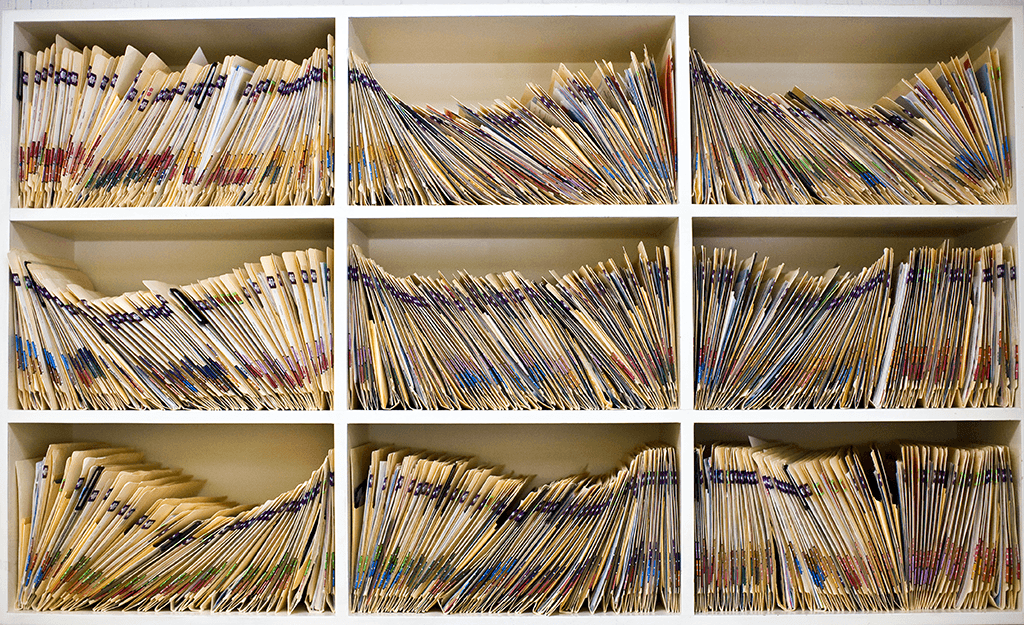
Generally, if a business handles protected health information, they need to be HIPAA-compliant. Protected health information can include anything from billing information, discussions between a patient and a doctor, and any medical data on file. HIPAA law describes these businesses as covered entities or business associates.
Covered entities includes U.S. health plans, health care clearinghouses (generally billing and data collection), and health care providers, but these trickle down even further. For instance, if your employer submits any personal health information to their health plan for you, they need to be compliant.
Business associates covers vendors of any of the above organizations who have access to the personal health information of patients. A couple of examples of business associates affected by the Health Insurance Portability and Accountability Act would be medical transcription companies, independent accountants, and data storage companies like WHOA.com.
WHOA.com has been verified as HIPAA compliant by an independent auditor. Its cloud-based infrastructure is apt to handle any and all patient information with the utmost in security and privacy.
Contact WHOA.com today to see how they can help your firm customize and configure your own private cloud environment.